To stay safe, you need more than just a fast server. You need a strategy that layers technical safeguards with real-time monitoring. This guide breaks down how to implement slashing avoidance and keep your assets secure.
What Exactly is Slashing and Why Does it Happen?
In a PoS system, Slashing is a penalty mechanism that removes a portion of a validator's stake as a punishment for malicious or negligent behavior . It's the network's way of ensuring everyone plays fair. If you try to cheat the system or are simply too careless with your hardware, the protocol burns your funds or redistributes them.
While every chain handles it differently, most slashable offenses fall into three buckets:
- Double-signing: This is the cardinal sin. It happens when a validator proposes or signs two different blocks for the same slot. It often occurs if you accidentally run the same validator keys on two different servers.
- Surround Voting: Common in Ethereum, this happens when a validator attests to two conflicting checkpoints, essentially lying about the state of the chain.
- Downtime: While less severe than double-signing, missing too many blocks (like 32 consecutive epochs in Ethereum) can lead to "inactivity leaks" where you slowly lose funds.
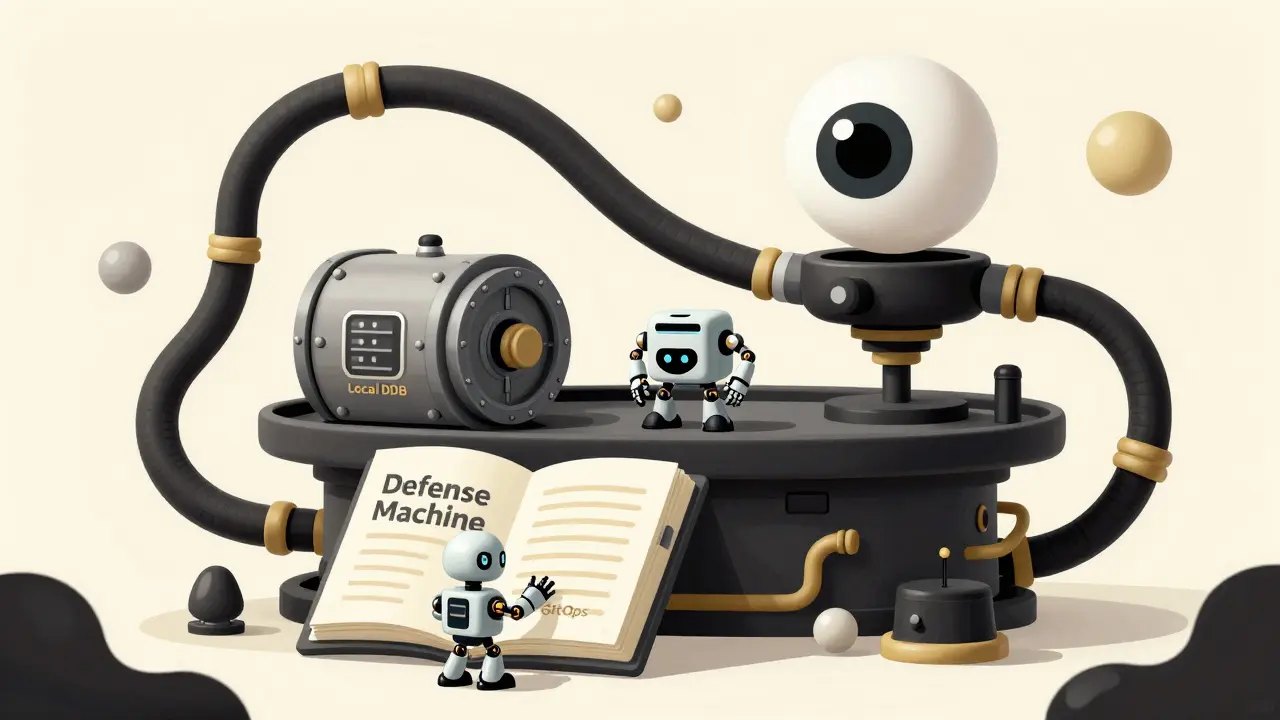
The Three-Layer Defense Strategy
You can't rely on a single piece of software to protect you. The industry gold standard, popularized by frameworks like Kiln, uses a tiered approach to ensure that even if one layer fails, your keys don't sign a slashable message.
Layer 1: GitOps and Deployment Validation
Prevention starts before the server is even live. By using GitOps, you can run continuous integration (CI) checks that scan your deployment scripts. These checks ensure you aren't accidentally deploying the same validator key to multiple environments (e.g., accidentally launching a "test" server with "mainnet" keys). If a duplicate is detected, the deployment is automatically blocked.
Layer 2: Local Anti-Slashing Databases
Your validator client should maintain a local record of every block and attestation it has ever signed. Before the client signs a new block, it checks this database. If it sees that a signature for that specific slot already exists, it refuses to sign. This is your primary defense against accidental double-signing caused by software restarts or crashes.
Layer 3: External Signing Authorities
For those running multiple nodes, a local database isn't enough. You need a global coordination layer. An external signing authority acts as a "gatekeeper" that manages a global database. No matter how many clients you have, they all must clear their signature with this central authority first. This architecture has been shown to reduce slashable offenses by over 99% in large-scale deployments.
| Network | Double-Signing Penalty | Downtime Penalty | Recovery Possibility |
|---|---|---|---|
| Ethereum | Severe (up to 5% burn + removal) | Moderate (Inactivity leak) | Permanent Removal (Tombstoning) |
| Cosmos Hub | High (5% slashing) | Low (0.01% penalty) | Permanent Removal |
| Solana | High (5% burn) | Reputation-based / Low | Permanent Removal |
| Near Protocol | Variable | Low | Recoverable after 36 hours |
Hardware and Infrastructure Requirements
You can't run a professional validator on a cheap laptop. Infrastructure instability is the leading cause of downtime penalties. To avoid these, you need a setup that prioritizes uptime and data integrity.
For enterprise-grade stability, follow these minimum specifications suggested by the Proof-of-Stake Alliance:
- CPU: 8-core processors to handle the heavy lifting of consensus calculations.
- RAM: Minimum 32GB. Memory leaks can crash a node, leading to missed attestations.
- Storage: 1TB NVMe SSD. Standard HDDs are too slow for the high I/O requirements of modern blockchain databases.
- Key Management: Use Hardware Security Modules (HSMs) to store your private keys. This prevents keys from being leaked or accidentally copied across servers.
Additionally, consider using geographically distributed sentry nodes. If your primary data center goes dark due to a power outage, a sentry node in another region can help maintain your connection to the peer-to-peer network, preventing a total blackout that would trigger downtime penalties.
Setting Up a Proactive Monitoring Stack
If you wait for a notification that you've been slashed, it's already too late. You need a monitoring system that tells you when you are about to be slashed. Most pros use a combination of Prometheus for data collection and Grafana for visualization.
Your dashboard should track these specific critical metrics:
- Time Since Last Attestation: If this exceeds 30 slots, you have a critical problem. Set an alert to trigger at 15 slots so you have time to react.
- Missed Attestations per Epoch: A warning should trigger if you miss more than 3 attestations. This is often a sign of network instability or CPU throttling.
- Validator Balance: Any unexpected decrease in your balance is a red flag. It could be a minor penalty or the start of a larger slashing event.
- Peer Connectivity: Monitor how many peers your node is connected to. If this drops significantly, you may be experiencing a network partition.
The goal is a sub-500ms response time. When an alert hits your phone, you should be able to pivot to a backup node or restart a service within minutes, not hours.

Common Pitfalls and How to Fix Them
Even experienced operators run into trouble. One of the most common issues is database corruption in local anti-slashing systems. When the database corrupts, the validator may "forget" what it signed and accidentally sign the same block again.
To fix this, implement daily automated backups of your slashing protection database. Perform a corruption check every 24 hours. If the check fails, you can restore from a backup before the validator client starts signing again.
Another risk is "correlated slashing." This happens when a large group of validators all use the same flawed software version or the same crashing cloud provider. In Ethereum, if a huge percentage of validators fail at once, the penalty is actually harsher. To avoid this, diversify your infrastructure. Don't put all your nodes in one AWS region. Mix your cloud providers or use a combination of bare metal and cloud services.
Can I recover my funds after being slashed?
In most cases, no. Slashing is designed to be a permanent economic penalty. In Ethereum, a severe slash leads to "tombstoning," where the validator is permanently removed from the network. However, some networks like Near Protocol allow for temporary slashing where funds can be recovered after a specific period (e.g., 36 hours) for minor infractions.
Is it safer to use a staking service or run my own node?
Staking services like Coinbase Cloud or Kiln generally offer higher security because they provide enterprise-grade slashing protection, including the three-layer defense and 24/7 monitoring. DIY validators have significantly higher "near-miss" rates because they often lack the infrastructure for real-time alerting and global signing coordination.
What is the difference between a penalty and slashing?
A penalty is typically a small fine for minor issues, like missing a few blocks (downtime). Slashing is a severe punishment for critical security violations, like double-signing. While a penalty might cost you a few cents of your reward, slashing can take a percentage of your entire principal stake.
How often should I update my validator software?
Updates should be performed carefully. While staying current is important for security and performance, updating in the middle of a network peak can cause instability. Always test updates on a testnet first. Use a rolling update strategy if you have multiple nodes to ensure the network remains stable.
Does hardware failure always lead to slashing?
Not necessarily. A simple crash usually leads to downtime penalties, which are relatively small. However, if a hardware failure causes a database corruption that leads to double-signing upon restart, that will trigger a severe slash. This is why local anti-slashing databases and backups are so critical.
Next Steps for Every Validator
If you're just starting, don't jump straight into the deep end. Start by spending a few dozen hours studying the consensus layer of your chosen chain. Ethereum, for instance, requires a deeper understanding of epochs and slots than simpler chains.
Your immediate roadmap should be:
- Audit your keys: Ensure no single key is used on more than one active machine.
- Deploy Monitoring: Set up Prometheus and Grafana. If you can't see your missed attestations in real-time, you're flying blind.
- Backup Strategy: Automate your database backups and test a recovery scenario to see how long it takes you to get back online.
- Diversify: If you're running multiple nodes, move them to different data centers to avoid correlated failure.






Write a comment