Imagine you run a business with a modern VoIP system. You have high-speed internet, top-tier headsets, and a reliable PBX. Yet, calls still drop during peak hours, or worse, your network gets hit by a denial-of-service attack that silences every line at once. The problem isn't usually your phone hardware; it's the lack of a proper gatekeeper between your private network and the chaotic public internet. That is where the Session Border Controller, commonly known as an SBC, comes in.
An SBC is not just another firewall. It is a specialized network element designed specifically to protect, regulate, and facilitate IP communications flows. While traditional firewalls block traffic based on ports and IP addresses, an SBC understands the actual content of the voice call. It reads the signaling protocols, manages the media streams, and ensures that only authorized, high-quality conversations pass through your network border. In this guide, we will break down what an SBC does, how its architecture works, and exactly how it handles a call from start to finish.
The Core Role of an SBC in VoIP Networks
To understand why you need an SBC, you first need to understand the vulnerabilities of Voice over Internet Protocol (VoIP). Unlike traditional landlines, VoIP runs over standard data networks. This means your voice traffic shares the same path as your email, web browsing, and file transfers. Without protection, this openness invites trouble.
The primary role of an SBC is to act as a router and gatekeeper between different network domains. Think of it as a bouncer for your communication infrastructure. According to industry definitions, an SBC sits inline between your company's internal VoIP network and the larger Wide Area Network (WAN) or external carrier networks. Its job is to ensure that the session parameters are correct before allowing the call to proceed.
This role has evolved significantly. Early deployments focused solely on peering environments-where two service providers connected their networks. Today, SBCs are critical in hybrid setups, connecting enterprise LANs to cloud-based Unified Communications (UC) platforms, residential access networks, and mobile networks like VoLTE (Voice over LTE). Whether you are using SIP (Session Initiation Protocol), H.323, or MGCP, the SBC ensures interoperability and security across these diverse systems.
- Security: Protects against unauthorized access, DDoS attacks, and toll fraud.
- Interoperability: Bridges different protocols and codecs between disparate systems.
- Quality Management: Enforces QoS policies to prevent jitter and latency issues.
- Regulatory Compliance: Supports emergency services (E911) and lawful interception.
Key Functions: More Than Just a Firewall
While many people confuse SBCs with Application Layer Firewalls (ALFs), they offer a broader set of capabilities tailored specifically for real-time communications. Let's look at the specific functions that make an SBC indispensable.
Access Control and Topology Hiding
One of the biggest risks in VoIP is exposing your internal network structure to the outside world. If an attacker can see your internal IP addresses, server names, and device types, they have a roadmap for launching targeted attacks. An SBC provides topology hiding. When an external party sends a request, the SBC strips out internal details and presents itself as the endpoint. The external caller never knows your PBX exists; they only talk to the SBC. This prevents reconnaissance attacks and hides your internal architecture from potential threats.
Protocol Translation and Normalization
The VoIP world is fragmented. One vendor might use strict SIP standards, while another uses proprietary extensions. Legacy systems might rely on H.323, while modern cloud platforms demand SIP. An SBC acts as a translator. It normalizes SIP headers and messages to mitigate multivendor incompatibilities. For example, if your internal system sends a malformed SIP message, the SBC can fix it before passing it to the carrier, preventing call failures due to syntax errors.
Codec Transcoding
Different networks prefer different ways to compress voice data. Your office might use G.711 for high-fidelity audio, while a remote branch office uses G.729 to save bandwidth. Without an SBC, these two parties couldn't talk because they speak different "audio languages." The SBC performs codec transcoding, converting the media stream from one format to another in real-time. This ensures compatibility and maintains call quality regardless of the underlying network constraints.
NAT Traversal
Network Address Translation (NAT) is essential for home and small business networks to conserve IPv4 addresses, but it is a nightmare for VoIP. SIP packets contain IP addresses inside their payload. When a packet passes through a NAT device, the outer IP changes, but the inner IP remains the same, causing the call to fail. SBCs facilitate NAT traversal by modifying the SIP headers and managing the media paths so that voice packets can find their way back to the originator, even when hidden behind multiple layers of NAT.
SBC Architecture: Proxy vs. B2BUA
Not all SBCs work the same way. The architectural approach determines how much control the SBC has over the call and how it impacts network performance. There are two primary models: the Proxy model and the Back-to-Back User Agent (B2BUA) model.
| Feature | Proxy Model | B2BUA Model |
|---|---|---|
| Signaling Control | Forwards signaling between endpoints | Terminates inbound leg, initiates outbound leg |
| Media Path | Direct between endpoints (usually) | Flows through the SBC |
| Topology Hiding | Limited (depends on implementation) | Complete (internal topology fully hidden) |
| Latency Impact | Low | Moderate (due to processing) |
| Transcoding Capability | No (cannot process media) | Yes (can transcode codecs) |
| Call Admission Control | Limited visibility | Full control and enforcement |
In the Proxy model, the SBC simply inspects and forwards the signaling messages. It helps with NAT traversal and basic security but allows the media (voice) to flow directly between the caller and receiver. This reduces latency and server load but offers less control over call quality and security.
In the Back-to-Back User Agent (B2BUA) model, the SBC terminates the incoming call and creates a new outgoing call. It sits in the middle of both the signaling and media paths. This gives the SBC complete visibility and control. It can enforce Call Admission Control (CAC), monitor quality in real-time, and perform transcoding. Most enterprise-grade deployments use the B2BUA model because the security and quality benefits outweigh the slight increase in latency.
Understanding the VoIP Call Flow with an SBC
Seeing the theory is one thing; seeing the action is another. Let's walk through a typical call flow using the Session Initiation Protocol (SIP) in a B2BUA architecture. We'll assume an employee (Alice) inside the corporate network calls a client (Bob) on the public PSTN.
- INVITE Request: Alice picks up her phone and dials Bob's number. Her IP phone sends a SIP INVITE message to the internal PBX. The PBX routes this request to the SBC because Bob is an external number.
- Authentication and Policy Check: The SBC receives the INVITE. First, it checks if Alice is authorized to make this type of call. Is she allowed to call international numbers? Does the network have enough bandwidth? If the answer is no, the SBC rejects the call immediately with a "403 Forbidden" or "486 Busy Here" response, saving resources.
- Topology Hiding and Header Manipulation: Assuming the call is authorized, the SBC strips Alice's internal IP address and any sensitive header information. It replaces them with its own external IP address. This hides the internal network from Bob's side.
- Protocol Conversion (if needed): If the internal network uses one protocol and the carrier uses another, the SBC translates the signaling. It also negotiates the codec. If Alice prefers G.711 but the carrier only supports G.729, the SBC agrees to G.729 with the carrier and tells Alice it will handle the conversion.
- New Leg Establishment: The SBC generates a new SIP INVITE message addressed to the carrier network. This is a fresh session, independent of Alice's original request.
- Ringing and Media Setup: The carrier finds Bob's phone and sends ringing signals back to the SBC. The SBC translates this into a ringing signal for Alice. Once Bob answers, the media path is established. In a B2BUA setup, Alice's voice goes to the SBC, which may transcode it, and then sends it to the carrier. Bob's voice follows the reverse path.
- Call Termination: When either party hangs up, a BYE message is sent. The SBC ensures that both legs of the call (internal and external) are properly torn down, releasing resources and logging the call detail record (CDR) for billing and analytics.
Quality of Service and Call Admission Control
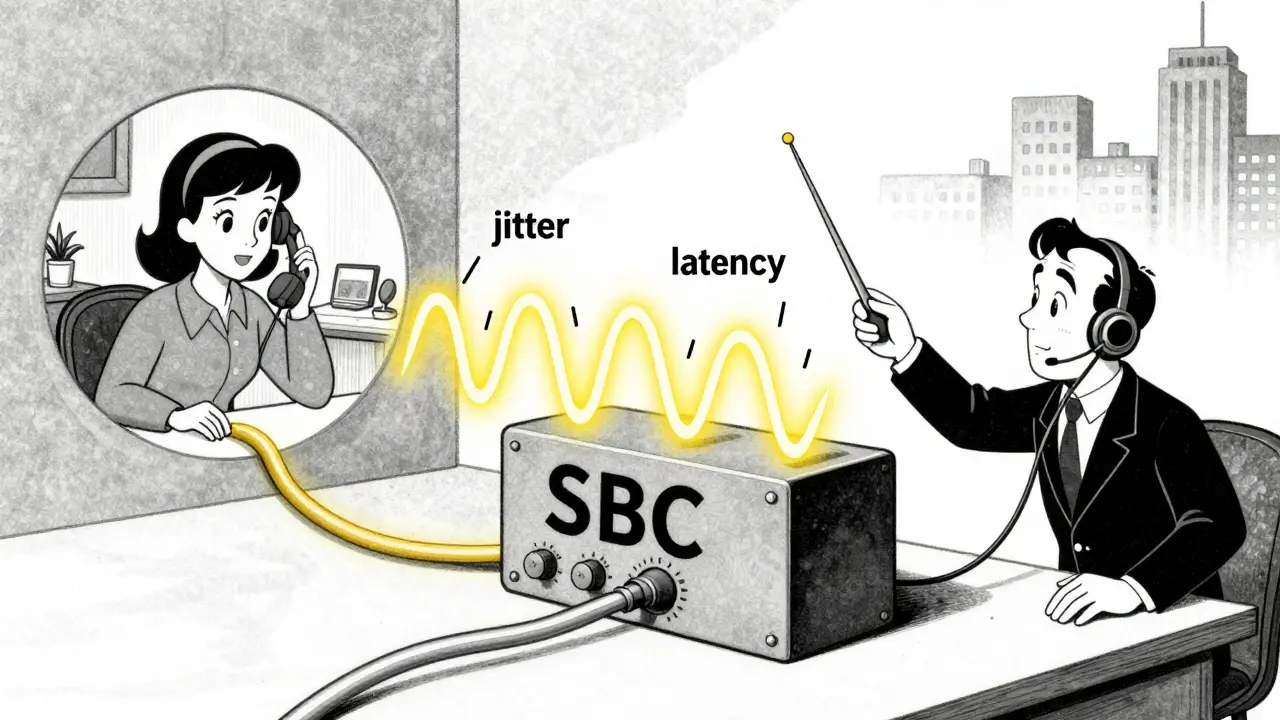
A secure network is useless if the call quality is poor. This is where Call Admission Control (CAC) and Quality of Service (QoS) management become critical. VoIP is sensitive to latency, jitter, and packet loss. A delay of more than 150 milliseconds can make a conversation feel unnatural.
The SBC monitors the network conditions in real-time. Before allowing a new call, CAC checks if there is sufficient bandwidth available. If the link is congested, the SBC can reject new non-emergency calls to preserve quality for active conversations. It also marks packets with Type of Service (ToS) or Differentiated Services Code Point (DSCP) bits. These markers tell routers along the path to prioritize voice traffic over less time-sensitive data like email downloads.
Furthermore, the SBC can detect and mitigate issues mid-call. If it detects excessive jitter, it can adjust buffer sizes or switch to a more robust codec dynamically. This proactive management ensures that callers experience consistent clarity, reducing dropped calls and improving user satisfaction.
Emergency Services and Regulatory Compliance
In telecommunications, reliability isn't just about convenience; it's about safety. Many regulatory bodies require VoIP providers to support emergency services, such as E911 in North America or 112 in Europe. Standard VoIP systems often struggle to locate callers accurately because IP addresses don't always correspond to physical locations.
An SBC plays a vital role here. It can be configured to recognize emergency dial codes and route them with the highest priority, bypassing normal congestion controls. It can also inject location data into the SIP headers, ensuring that emergency responders receive the correct address. Additionally, for service providers, SBCs provide lawful interception capabilities, allowing authorities to monitor calls legally when required by law. This compliance layer is non-negotiable for businesses operating in regulated industries.
Choosing the Right SBC Deployment
When implementing an SBC, you have choices regarding form factor and placement. You can deploy an SBC as a physical appliance, a virtual machine (vSBC), or as a cloud-based service. Physical appliances offer dedicated hardware performance and are common in large service provider cores. Virtual SBCs provide flexibility and scalability, making them ideal for enterprises with dynamic workloads. Cloud SBCs are gaining popularity for organizations moving entirely to UCaaS (Unified Communications as a Service) platforms, offloading the complexity of border control to the provider.
The decision depends on your scale, budget, and technical expertise. For most mid-sized enterprises, a virtual SBC deployed at the edge of the network offers the best balance of control and manageability. Regardless of the form, the core functions remain the same: securing the border, ensuring interoperability, and maintaining call quality.
What is the difference between an SBC and a firewall?
A traditional firewall operates at the network and transport layers, blocking traffic based on IP addresses and port numbers. It does not understand the content of the traffic. An SBC operates at the application layer, understanding VoIP protocols like SIP. It can inspect call logic, manage media streams, hide network topology, and perform protocol translation, which a standard firewall cannot do.
Do I really need an SBC if I use a cloud PBX?
Yes, especially if you have on-premise devices or legacy systems. Even with a cloud PBX, your local network needs protection from external threats and must handle NAT traversal correctly. An SBC ensures that your local endpoints connect securely and reliably to the cloud service, providing quality monitoring and security that the cloud provider cannot enforce on your local LAN.
How does an SBC improve call quality?
An SBC improves call quality through Call Admission Control (CAC), which prevents network overload by rejecting calls when bandwidth is low. It also enforces QoS policies by marking voice packets for priority handling. Additionally, it can perform codec transcoding to ensure compatibility and reduce bandwidth usage, and it mitigates jitter and latency issues through intelligent buffering and routing.
What is topology hiding in VoIP?
Topology hiding is a security feature where the SBC removes internal network information (like IP addresses, server names, and device types) from SIP headers before sending them to external networks. This prevents attackers from mapping your internal infrastructure, reducing the risk of targeted attacks and vulnerabilities.
Can an SBC prevent toll fraud?
Yes. Toll fraud occurs when hackers exploit VoIP systems to make expensive long-distance or premium-rate calls. An SBC can be configured with strict access control lists (ACLs) and call patterns to block unauthorized destinations. It can also limit the number of simultaneous calls and monitor for unusual calling behavior, alerting administrators to potential fraud attempts.







Write a comment