Voice over Internet Protocol has transformed how businesses communicate, collapsing phone networks onto standard data infrastructures. This convenience comes with a steep price. When you run voice traffic over the same cables as your email and database traffic, you expose telephony protocols to the same threats that plague standard web servers. Attackers don't need a sophisticated war room to exploit these gaps; they need basic knowledge of signaling standards and a few open ports. By 2026, the convergence of data and voice means a breach in one often compromises the other completely.
A typical security audit misses half the problems because it treats the network as a single blob. It looks at HTTP and HTTPS but ignores Session Initiation Protocol(SIP), the language phones use to set up calls. An unsecured SIP server is like leaving your front door unlocked while installing alarms on the kitchen cabinets. We need a specialized approach to find where the walls are thin before the bad actors do.
Core Goals of VoIP Security Assessment
The objective isn't just to find "vulnerabilities" in a vacuum. You want to know if someone can eavesdrop on executive calls, hijack user identities, or rack up massive international toll fraud charges on your dime. A proper assessment verifies three layers:
- Infrastructure Integrity: Is the network segmentation actually separating voice from general data traffic?
- Protocol Hardening: Are Real-time Transport Protocol(RTP) streams encrypted, or is the audio flowing in plain text?
- Authentication Controls: Can a tester register a fake phone and make calls as the CEO?
If you treat VoIP security as just another checkbox on a compliance form, you leave the back door wide open. The stakes are real because voice traffic often carries sensitive information about ongoing deals, legal matters, or personal schedules.
Methodology: How We Break Into Systems Safely
We follow a structured path based on the Penetration Testing Execution Standard (PTES). However, standard web testing doesn't work perfectly for telephony. Here is the flow we use to systematically uncover risks without breaking your business continuity.
Phase 1: Reconnaissance
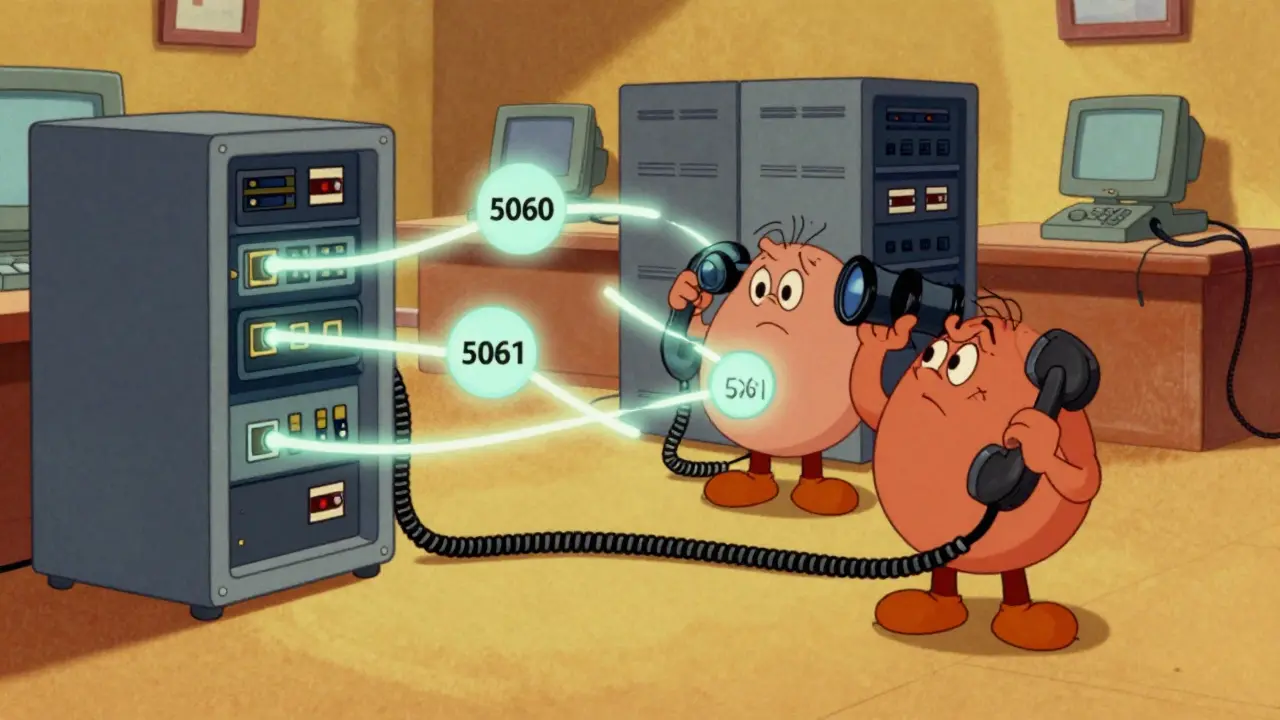
This step is about finding the targets. We scan for active IP addresses running on specific ports-usually UDP or TCP port 5060 for SIP signaling. We look for devices that announce themselves. In a messy network environment, an unmanaged Private Branch Exchange(PBX) might broadcast its existence to anyone listening on the subnet. We use passive listening combined with active scanning to map out which extensions belong to which users.
Phase 2: Threat Modeling
Before running exploits, we decide what matters most. For some clients, data privacy is paramount (encryption failure is the biggest risk). For others, availability is king (they fear denial-of-service attacks dropping their call centers). Understanding your priority dictates which vectors we test more aggressively.
Phase 3: Vulnerability Analysis
Here is where we probe the specific protocol behaviors. Does the system require strong encryption when setting up a TLS connection? If we send a request without encryption, does it accept it anyway? We also check for weak cipher suites that older phones might force the server to downgrade into.
Phase 4: Exploitation
This is the controlled attack phase. We try to register unauthorized endpoints, intercept media streams, or perform caller ID spoofing. We document exactly how much effort is required to compromise the system. If it takes ten minutes to gain access to the voicemail system, that is a critical finding.
Phase 5: Reporting
We deliver a clear action plan. Vendors often release patches for known issues, and configuration hardening guides can eliminate many risks immediately. Our report prioritizes fixes based on the likelihood of exploitation and the potential impact on your operations.
The Toolkit: Essentials for VoIP Audits
You cannot audit what you cannot measure. While general networking tools help, you need specific software designed for the quirks of telephony traffic. The following stack forms the backbone of our testing capability.
| Tool Name | Primary Function | Use Case Example |
|---|---|---|
| Nmap | Network Discovery & Port Scanning | Scanning for open SIP ports (5060/5061) across the network. |
| Wireshark | Packet Capture & Analysis | Decoding RTP streams to view call setup details in real-time. |
| SipVicious | SIP Enumeration & Attacks | Fuzzing SIP headers and brute-forcing extension numbers. |
| Metasploit | Exploitation Framework | Utilizing modules like viproy for broader vulnerability checks. |
| SSLScan | Certificate Validation | Verifying TLS configurations on secure SIP connections. |
Wireshark remains the gold standard for visualizing traffic. Its ability to decode SIP headers allows us to see exactly who called whom and where the call terminated. We can spot plaintext passwords embedded in the INVITE messages instantly. Without this visibility, a misconfigured firewall or weak authentication scheme stays hidden in the noise.
**SipVicious** takes a different angle. It automates the discovery of extensions. Imagine trying to guess every employee's extension number manually; SipVicious automates this by iterating through ranges and observing the server's response codes. If the server responds differently for a valid extension versus an invalid one, we know we have successfully enumerated the target list.
For deeper system compromise testing, the **Metasploit** framework includes modules specifically tailored for legacy telephony hardware. Many organizations still run older firmware versions on their desk phones. These often contain remote code execution vulnerabilities that Metasploit can validate safely.

Common Attack Vectors We Hunt For
Attackers focus on the path of least resistance. In VoIP environments, the most common weaknesses appear in the handling of identity and media.
SIP Enumeration
This involves discovering active users within a PBX. Many administrators fail to randomize extension numbers. If extensions run sequentially (1000 to 1999), an attacker can quickly map out the entire organization. By flooding the server with OPTIONS requests, they can verify which extensions are reachable and gather user-agent details (which tells us the manufacturer and model of the phone).
Caller ID Spoofing
This is perhaps the most frustrating issue for customer-facing businesses. An attacker modifies the 'From' header in the SIP packet before sending it to your gateway. Your display shows "Internal Support," but the call originates from outside the network. This undermines trust and facilitates social engineering attacks against staff.
RTP Stream Hijacking
If Real-time Transport Protocol is not encrypted (using SRTP), the audio data travels in clear text. On a shared network segment, any device can listen to these streams. An attacker simply filters for the stream address and begins recording conversations in real time. This bypasses all application-level encryption because the decryption happens inside the phone itself.
Toll Fraud via Registration
Weak password policies on phone registrars allow attackers to register their own softphone with stolen credentials. Once registered, they can route outbound calls to premium-rate numbers. The damage is financial and immediate, often detected only days later when the billing cycle closes.
Remediation Strategies That Work
Finding holes is half the battle; closing them effectively is the rest. Remediation requires both policy changes and technical adjustments.
Enforce Network Segmentation: Move VoIP traffic to a dedicated VLAN. Implement Access Control Lists (ACLs) on the router so that voice devices can talk to the PBX and the internet, but cannot talk to internal file servers or HR databases. This containment stops lateral movement.
Mandate Encryption: Disable standard SIP usage globally unless absolutely necessary for legacy reasons. Configure all gateways and PBX units to enforce TLS for signaling and SRTP for media. This ensures that even if traffic is intercepted, it is unintelligible gibberish to the attacker.
Hardening Authentication: Implement multi-factor authentication (MFA) for administrative interfaces. Change default credentials on all devices immediately upon installation. Use complex passwords for SIP accounts that prevent dictionary attacks.
Regular Firmware Updates: Telecommunications hardware vendors release security patches regularly. Establish a cadence for updating PBX servers and endpoint phones. Outdated firmware is the easiest entry point for automated bots scanning the internet.

Frequently Asked Questions
Why is VoIP penetration testing different from standard web testing?
VoIP relies on real-time transport protocols like RTP and SIP rather than HTTP. Web scanners often miss these stateful communication sessions. Specialized analysis is needed to inspect media streams and signaling handshakes, which function differently from standard web forms or API calls.
Can VoIP be hacked without physical access?
Yes. Because VoIP runs over the public Internet or corporate WANs, attackers can reach services remotely. If ports like 5060 are exposed to the internet without strict firewall rules, remote attackers can attempt enumeration or brute-force registration attempts.
What is the most critical VoIP vulnerability?
Unencrypted media streams (RTP) are often the highest risk. They allow eavesdropping on live conversations. Additionally, missing authentication on the PBX interface can lead to immediate total takeover and toll fraud.
How often should we conduct these tests?
You should run full penetration tests annually. However, whenever you update firmware, change network topologies, or add new sites, you should run a quick verification scan to ensure new assets haven't introduced gaps.
Do cloud-hosted PBX solutions still need testing?
Absolutely. While the provider secures the backend, your local network (endpoints and internet connection) remains under your control. Misconfigurations on your side often provide the path to compromise the service.
Next Steps and Implementation Roadmap
If you suspect your current setup is vulnerable, start by checking your router logs. Look for failed login attempts on ports 5060 or 5061. If you see activity from IP addresses you don't recognize, your perimeter may already be compromised. Engage a qualified professional to run a full assessment before assuming the risk. Insecurity is not an option when dealing with critical communications infrastructure.







Rajashree Iyer
28 Mar 2026 at 03:55The silence of the network is deceptive because it masks the chaos underneath the protocol headers.
We see the data flowing but we ignore the voices whispering secrets in the clear text packets.
This is how empires fall quietly without a single gunshot fired in the physical realm.
A phone system is not just hardware anymore but it is a portal into the soul of communication.
If we leave RTP open then we hand the microphone to every listener on the street corner.
The encryption keys are lost before anyone even realizes the stream was intercepted.
We build walls around the database yet the voice traffic slips through the cracks unnoticed by the guard towers.
SIP is the language of trust yet it speaks in plain sight to the wolves waiting outside.
You cannot patch your way through a philosophy that ignores the fundamental nature of convergence.
Imagine the executive conversations turning into public broadcasts across the unsecured internet backbone.
It feels wrong to let money flow so easily when the toll fraud scripts are waiting for input.
There is a moral decay in allowing these protocols to remain exposed for the sake of convenience.
We must treat the packet capture tool as an extension of human perception rather than just a utility.
The vulnerability lies not in the code but in the assumption that data stays within the server room.
Every call setup request is a handshake that invites potential betrayal from the other side.