When your team works from home, coffee shops, or airports, your phone calls aren’t safe just because they’re digital. Without encryption, anyone on the same Wi-Fi network can listen in-record conversations, steal customer data, or even make expensive international calls using your company’s line. This isn’t science fiction. In 2023, a small accounting firm lost $17,500 in fraudulent charges after an employee used an unsecured home network for VoIP calls. The fix? A properly configured VPN for VoIP.
Why VoIP Needs a VPN
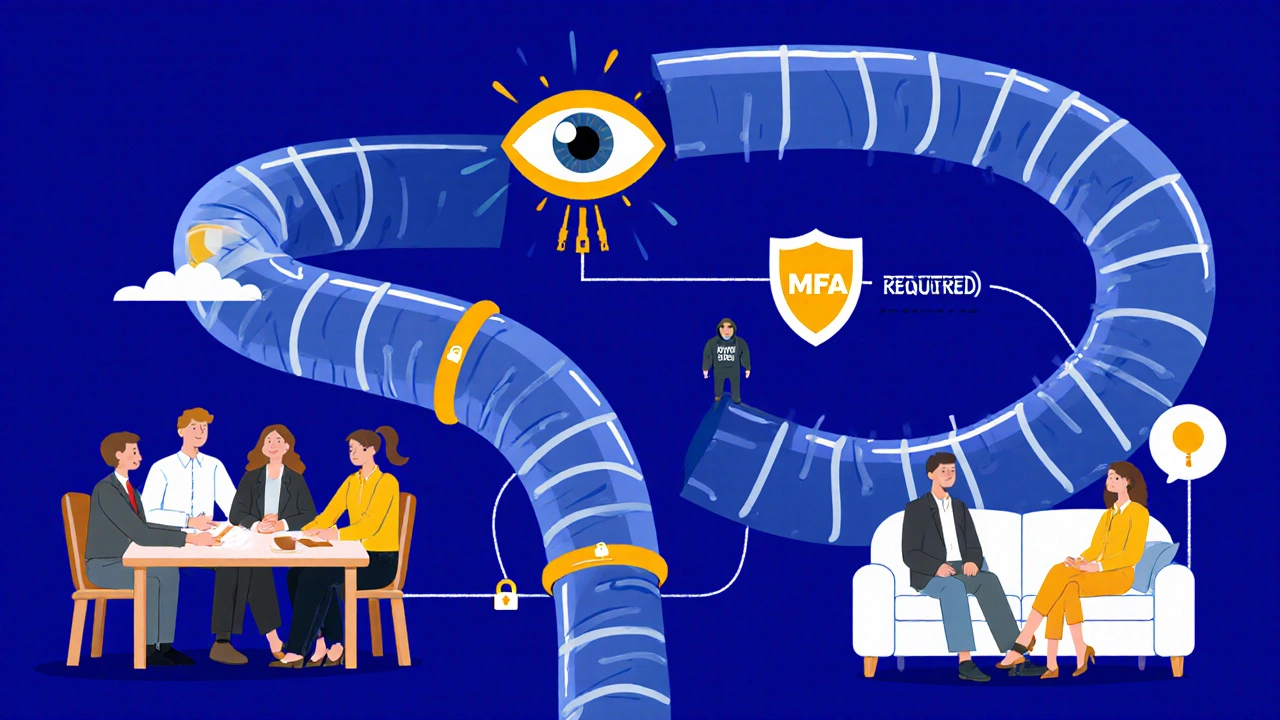
VoIP turns your voice into data packets that travel over the internet. That’s convenient, but it’s also risky. Unlike traditional phone lines, which are physical and hard to tap, VoIP signals ride alongside your emails, streaming videos, and social media traffic. If someone intercepts those packets, they can replay your conversation, alter it, or block it entirely. A VPN creates a private tunnel between your device and your company’s phone system. It wraps every voice packet in encryption, so even if someone catches it, they see only scrambled junk. This isn’t optional anymore. With 74% of companies now running hybrid work models, securing remote calls isn’t a luxury-it’s a baseline requirement.What Gets Encrypted: Signaling vs. Media
Not all encryption is the same. VoIP has two parts: signaling and media. Signaling is the "hello, let’s talk" part-it sets up the call, tells the system who’s calling whom, and ends the call. Media is the actual voice you hear. Many people think TLS (Transport Layer Security) is enough. It’s not. TLS only encrypts signaling. Your voice? Still plain text. That’s like locking your front door but leaving your windows wide open. The real protection comes from SRTP (Secure Real-Time Transport Protocol). It encrypts the media stream-the actual voice. Combine SRTP with TLS, and you’ve got full coverage: call setup and voice content are both locked down. Cisco, Teledynamics, and Phonesuite.com all agree: SRTP is non-negotiable for secure VoIP.Choosing the Right VPN Protocol
Not all VPNs are built for voice. Consumer apps like NordVPN or ExpressVPN are designed for browsing and streaming-they don’t prioritize voice traffic. Use them for VoIP, and you’ll get choppy calls, dropped audio, or worse: no sound at all. For business use, two protocols stand out:- OpenVPN: Uses UDP (User Datagram Protocol), which is faster and more reliable for real-time voice. Teledynamics testing showed 18% better call quality than IPSec. It’s also easier to configure through firewalls.
- IPSec: Widely supported in enterprise gear, especially Cisco and Fortinet routers. It’s solid, but can be slower on unstable networks because it uses TCP for control signals.
Network Segmentation: Keep Voice Separate
Don’t mix your VoIP traffic with general internet use. If your employee’s laptop downloads a movie while on a client call, that video stream eats bandwidth and causes lag. Worse, if their device gets infected with malware, the attacker can now access your phone system. Solution? Use VLANs (Virtual LANs). This splits your network into separate lanes. One lane for voice, one for data. Even if malware gets on the data side, it can’t reach the voice side. According to 1stel.com’s survey of 147 mid-sized businesses, companies using VLANs saw 29% fewer VoIP security incidents. You don’t need fancy gear. Most business-grade routers (like Ubiquiti, Netgear Business, or Cisco RV series) support VLAN tagging. Just assign your VoIP phones and softphones to a dedicated VLAN, and set rules to restrict traffic between networks.Firewall Rules: The Silent Killer of VoIP Calls
Here’s the most common mistake: letting the VPN work but forgetting to open the right ports. VoIP uses two types of traffic:- SIP (Session Initiation Protocol): Usually on port 5060. This is for call setup.
- RTP (Real-time Transport Protocol): Uses dynamic ports between 16384 and 32768. This carries your voice.

Bandwidth and Quality of Service (QoS)
A single HD VoIP call needs about 100 kbps. That doesn’t sound like much. But if five people are on calls, streaming, and video conferencing over the same home internet, you’re at 1 Mbps-and that’s before other devices jump on. Without QoS (Quality of Service), your router treats all traffic equally. So when someone starts a Netflix binge, your call quality drops to robotic, glitchy noise. Enable QoS on your router and prioritize VoIP traffic. Most business routers let you assign priority by application (like "SIP" or "VoIP") or by device (your company phone). Set it to give voice traffic top priority. That way, even during peak usage, your calls stay clear.Authentication and MFA: Don’t Skip This
A VPN is only as strong as the login that opens it. If employees use weak passwords or reuse credentials, your whole system is at risk. Require multi-factor authentication (MFA) for every VPN connection. Use apps like Google Authenticator or Microsoft Authenticator-not SMS, which can be intercepted. Combine that with device compliance checks: only let company-managed devices connect. No personal phones. No unpatched laptops. Cisco AnyConnect and other enterprise solutions let you enforce these rules automatically. If a device hasn’t updated its OS in 30 days? Block access. If MFA isn’t enabled? Deny the login.Training and Human Risk
The biggest threat to VoIP security isn’t a hacker-it’s your employee. Phonesuite.com found that 68% of VoIP breaches start with social engineering. Someone gets a fake email: "Your phone system needs an update. Click here." They install malware. Suddenly, attackers have access to your call logs, recordings, and internal numbers. Train your team like you train them on phishing. Teach them:- Never click links in unsolicited emails about IT systems
- Verify caller IDs-scammers can spoof your own company number
- Report weird audio: echoes, delays, or sudden silence during calls
Cloud vs. On-Premise: What’s Right for You?
There are two paths:- Cloud-based VoIP with built-in security: Services like RingCentral, 8x8, or Zoom have encryption, MFA, and secure access built in. Setup is fast. No hardware. Good for small teams or startups.
- On-premise or hybrid with dedicated VPN: You control the encryption, the network, and the rules. Better for larger companies with compliance needs (HIPAA, GDPR, PCI-DSS). Requires more IT skill but gives full control.
Future Trends: Zero Trust and AI
The old model-"trust anyone inside the network"-is dead. Today’s best practices follow Zero Trust: verify every device, every user, every time, no matter where they are. New tools like ZTNA (Zero Trust Network Access) are replacing traditional VPNs. Instead of connecting to your whole network, users get access only to the apps they need-like your VoIP server. No lateral movement. No broad access. AI is also stepping in. Some vendors are testing systems that detect abnormal call patterns: a user suddenly calling 50 international numbers in 10 minutes? Flag it. A call from a device that’s never been used before? Block it until verified. These aren’t sci-fi. They’re already in beta at 37% of enterprise security teams.Implementation Checklist
Here’s what to do next:- Identify all remote workers using VoIP
- Choose SRTP + TLS for encryption
- Deploy OpenVPN or IPSec on business-grade routers
- Set up VLANs to separate voice and data traffic
- Open UDP ports 16384-32768 on your firewall for RTP
- Enable QoS to prioritize VoIP traffic
- Require MFA for all VPN logins
- Enforce device compliance (updated OS, antivirus)
- Train staff on phishing and call security
- Run quarterly security audits
What Happens If You Don’t Secure VoIP?
You might not notice until it’s too late. - Fraudulent international calls rack up $10,000+ in charges - Customer conversations are recorded and sold on the dark web - Regulatory fines hit for GDPR or HIPAA violations - Your team loses trust because calls feel "unsafe" The cost of a breach? Far higher than setting up a VPN. According to Gartner, the average cost of a VoIP-related security incident in 2023 was $42,000. A good VPN setup? Under $50 per user per year.Final Thought
VoIP is the new office phone line. And just like you wouldn’t leave your front door unlocked, you shouldn’t leave your voice calls exposed. A properly configured VPN isn’t just a tech upgrade-it’s a trust signal to your customers, your team, and your regulators. The tools exist. The standards are clear. The cost of inaction is high. Start securing your calls today-not because it’s trendy, but because your business depends on it.Can I use a consumer VPN like NordVPN for VoIP calls?
No. Consumer VPNs aren’t designed for voice traffic. They often block or delay RTP ports, cause high packet loss, and don’t prioritize call quality. You’ll get dropped calls, lag, or no audio. Use enterprise-grade solutions like OpenVPN or Cisco AnyConnect instead.
Does a VPN slow down VoIP calls?
A well-configured VPN adds 15-40ms of latency, which is still within the ITU-T G.114 standard (under 150ms one-way). That’s barely noticeable. Poorly configured ones can cause delays because of bandwidth hogging or firewall missteps. Always use QoS to keep voice traffic moving smoothly.
What’s the difference between TLS and SRTP?
TLS encrypts the call setup (signaling)-who’s calling whom. SRTP encrypts the actual voice (media). Using TLS alone leaves your conversation open to eavesdropping. Always use both: TLS for signaling, SRTP for voice.
Why do I hear ringing but no audio during calls?
That’s a classic firewall issue. SIP (port 5060) works, but RTP (ports 16384-32768) is blocked. Check your firewall rules to allow bidirectional UDP traffic on those ports for your VPN’s IP range. This fixes 43% of VoIP audio failures.
Do I need a special router for VoIP over VPN?
Yes. Consumer routers often lack VLAN support, QoS controls, and proper firewall customization. Use a business-grade router from Ubiquiti, Netgear Business, or Cisco. These let you segment traffic, prioritize voice, and open the right ports safely.
Is VoIP encryption required by law?
It depends. If you handle health data (HIPAA), payment info (PCI-DSS), or EU customer data (GDPR), encrypted VoIP is mandatory. Even if not legally required, it’s a best practice-and many clients expect it. Unencrypted calls risk fines, lawsuits, and reputational damage.
Can I use a cloud VoIP provider instead of a VPN?
Yes, if the provider offers end-to-end encryption and secure access. RingCentral, 8x8, and Zoom now include built-in SRTP and MFA. This is ideal for small teams. But if you need full control over your network, data residency, or compliance policies, a dedicated VPN is still better.
How often should I audit my VoIP security?
Quarterly. Organizations that run audits every three months see 3.2x fewer security incidents than those that don’t. Check for outdated firmware, open ports, weak passwords, and unauthorized devices. Use automated tools to scan your SIP servers and VPN logs.









Priyank Panchal
29 Nov 2025 at 07:37This whole article is just corporate fluff wrapped in technical jargon. You think SRTP and VLANs are magic bullets? Try running VoIP over a 2Mbps connection in rural India with 300ms latency. No amount of encryption fixes bad infrastructure. I've seen teams lose clients because their 'secure' calls kept dropping during peak hours. The real solution? Stop pretending remote work is just like the office.